How to Avoid Spa Booking Scams: The 2026 Engineering Guide
The contemporary maturation of the global health hospitality market has transitioned from an era of aesthetic novelty toward a period of rigorous functional specificity. For the institutional developer, the family office, or the sophisticated asset manager, traditional markers of luxury high-specification finishes or artisanal decor now function as baseline commodities rather than competitive advantages. In their place, a new hierarchy of value has emerged, centered on Operational Fidelity. Within the diverse landscape of hydrothermal tourism, the act of securing a restorative residency no longer exists merely as a leisure transaction; it operates as a high-stakes deployment of capital where success is dictated by the management of information integrity and the mitigation of digital entropy.
Identifying and executing resilient strategies for aquatic-based health requires moving beyond the hobbyist vernacular of traditional travel planning. We are witnessing the professionalization of wellness spaces, where the quality of technical hardening, ranging from encrypted payment gateways to the integrity of verified administrative domains,s determines the occupant’s financial and psychological security. For the senior strategist, the selection of a booking framework for an elite asset represents a high-stakes decision. This process begins with a deconstruction of the digital envelope, ensuring that procurement choices align with localized security stressors to prevent premature resource depletion through fraudulent interception.
As we move through 2026, systemic integrity defines the success of these occupancies specifically, the degree to which transactional configuration, domain-control failovers, and identity-verification protocols align to produce a frictionless procurement environment. This transition marks the end of the “trust-based” era of hospitality, replacing it with an era of structural utility. In this new paradigm, the capacity for cognitive reset and environmental hardening, in terms of the speed at which a system identifies a fraudulent vector, tor measures the true authority of a development. This editorial analysis deconstructs the mechanics of elite hospitality administration and identifies the points of failure that compromise the promise of a secure sanctuary.
Understanding “how to avoid spa booking scams”

To grasp the full scope of how to avoid spa booking scams, one must view the modern high-end restorative residency not as a static luxury object, but as a metabolic system operating at the intersection of digital precision, behavioral economics, and hospitality. At its core, the term represents the strategic alignment of informational assets, sets verified domains, two-factor authentication, and blockchain-verified reservations with specific performance outcomes in environments characterized by high financial turnover and informational vulnerability. In commodity marketing, “avoiding scams” is frequently presented as a simple checklist of red flags. However, true optimization requires a radical departure from this view, acknowledging that high-end residency is a dynamic battle against the recurring expenses of digital wear and the high overhead of administrative infiltration.
A multi-perspective explanation reveals that while the primary goal remains the preservation of the inhabitant’s financial health, the secondary and tertiary goals involve the “Invisible Operation.” In elite management, developers entirely decouple booking protocols such as the verification of third-party aggregators or the calibration of secure server certificates from the inhabitant’s experience. The occupant should feel the value of the stay in the cognitive uptime it provides, while the rigorous battle against domain spoofing, social engineering, and utility instability remains obscured.
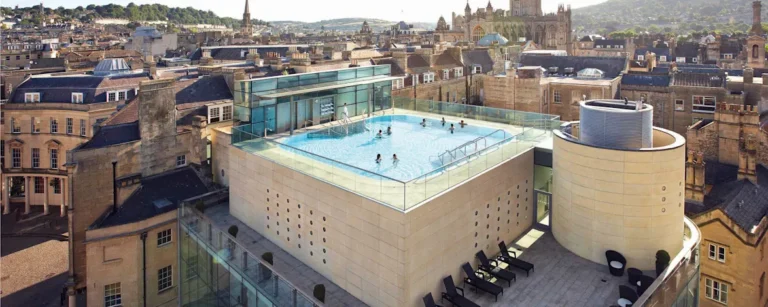
Common misunderstandings often conflate “visual prestige” with “transactional fidelity.” In the context of high-fidelity assets, superior experiences refer to the density of the security layer and the technical specificity of the infrastructure, not just the quality of the photography or the architectural pedigree of the site. Oversimplification risks are highest when stakeholders prioritize short-term convenience over long-term structural utility. A procurement choice that lacks redundant verification systems or professional-grade identity-management protocols cannot be classified as a secure development, regardless of the initial aesthetic appeal.
The Actuarial Evolution of Hospitality Fraud
The trajectory of hospitality procurement has shifted from a display of overt labor to an exercise in technical concealment. In the early 2010s, the presence of visible administrative staff performing manual confirmations signaled status; today, the presence of flawless utility flow, automated encryption,biometricetric integration signals true authority and fiscal maturity. This evolution mirrors the transition from trust-based systems to protocol-based systems.
Historically, owners of wellness sites relied on the individual loyalty of a facility manager or a small-scale booking agent. While effective in a simpler era, this model possessed a single point of failure. If the individual lacked technical knowledge of modern phishing vectors or gray-market arbitrage, the asset suffered. The modern era demands a decentralized stewardship model. Here, the knowledge is embedded in the software, the sensors, and the redundant protocols of the property itself. This shift ensures that the asset remains a high-performance node regardless of personnel turnover.
Systemic hardening now includes digital sovereignty alongside physical resilience. As aquatic sites integrate complex automation for pressure tracking and remote health monitoring, they become targets for digital intrusion. The contemporary site must therefore incorporate a technical firewall alongside its physical barrier. We no longer underwrite property based on menu diversity alone; we underwrite based on the metabolic health of the structure’s intesystemsl sys,tems its power redundancy, its moisture-intrusion integrity, and its capacity to maintain an unbroken “cold-chain” of transactional data.
Conceptual Frameworks for Transactional Sovereignty
To navigate the complexity of high-fidelity hospitality procurement, stewards should employ specific mental models that prioritize systemic resilience over aesthetic vanity.
1. The Domain Integrity Model
This framework treats the digital presence of the hotel as a biological organism with a specific DNA (the root domain). In high-use zones, the risk of “mutation” through sub-domain hijacking or look-alike URLs is significantly higher. Optimization involves identifying the “clogged arteries” of the operation, be it a legacy booking engine or an unverified third-party link that fails during peak occupancy.
2. The Information Asymmetry Theory
In elite hospitality, the scammer relies on the gap between what the property knows and what the inhabitant perceives. This theory prioritizes the management of the data differential. By maintaining a single, immutable source of truth for availability and pricing, the hotel prevents the migration of fraudulent data through the procurement envelope, which is the primary cause of resource depletion.
3. The Zero-Trust Protocol
Borrowed from cybersecurity engineering, this model dictates that every interaction (email, payment link, confirmation call) must be verified through at least two independent channels. In isolated retreat environments, this is non-negotiable. This prevents the cascading failure scenario where a single social-engineering breach leads to the loss of financial control, resulting in the rapid degradation of trust and structural integrity.
Key Categories of Procurement Risks
When evaluating the market for high-fidelity assets, stakeholders must recognize that fraud belongs to distinct archetypes, each requiring unique hardening strategies.
| Category | Primary Vector | Critical Failure Point | Hardening Priority |
| Domain Spoofing | Look-alike URLs | Browser Trust | DNSSEC / SSL Integrity |
| Social Engineering | Impersonation Calls | Human Psychology | Staff Training / Verification |
| Payment Hijacking | Unsecured Links | Financial Gateway | End-to-End Encryption |
| Gray-Market Resale | Unauthorized Aggregators | Inventory Control | Direct-Only Sovereignty |
Realistic Decision Logic
Before selecting a procurement or management framework, the property steward must rank the asset on a 1–10 scale across technical hardening and metabolic efficiency. A sum below 22 signals that a property requires significant operational capital before it can be certified as a secure sovereign node. Performance assets in high-stakes zones require 30% higher security budgets to maintain the same level of integrity as standard hospitality units.
Detailed Real-World Scenarios: Systemic Failure and Recovery
The Invisible DNS Breach
A high-resolution wellness property in a coastal zone experienced a slow failure of its domain registrar security.
-
The Failure: The property utilized a traditional password-based model. A “look-alike” site intercepted bookings for four months.
-
The Consequence: Fraudulent charges disabled the main payment processor’s trust score, requiring a $120,000 remediation and a total loss of occupancy for the east wing.
-
The Correction: Installing real-time domain monitoring that alerts for any new registrations mimicking the primary URL, reducing detection time from months to minutes.
The Social Engineering Failover
An estate focused on biological recovery relied solely on a single-point confirmation model for its high-value suites.
-
The Failure: A localized power outage forced staff to use unencrypted personal devices.
-
The Incident: Scammers intercepted the unencrypted communication, directing guests to a fraudulent payment portal.
-
The Second-Order Effect: Loss of $85,000 in revenue and a catastrophic drop in brand authority.
-
The Correction: Implementing a mandatory hardware-token-based 2FA for all administrative communications to ensure system uptime for data-critical zones.
Planning, Cost, and Resource Dynamics
The economics of high-fidelity hospitality aoften counterintuitivevee. Reducing the sticker price of a security framework often increases the total cost of ownership (TCO) due to accelerated environmental decay. In elite management, administrators entirely decouple cost-saving protocols such as automated transaction scrubbing from the inhabitant’s experience.
Range-Based Security and Management Investment (Monthly per Unit)
| Expense Item | “Standard” Market Plan | “High-Fidelity” Hardened Plan |
| Domain Stewardship | $100 – $200 (Reactive) | $800 – $1,500 (Predictive) |
| Transactional Auditing | $300 – $700 | $1,200 – $2,500 |
| Identity Management | $500 – $1,000 | $2,000 – $4,500 |
| Digital Security Ops | $200 – $400 | $800 – $1,500 |
A thorough process will reveal that the high-fidelity plan appears significantly more expensive on paper, yet it prevents the black swan events like mass identity theft or total financial breach that can cost hundreds of thousands in remediation and lost asset value.
Tools, Strategies, and Support Systems
-
DNSSEC Implementation: Ensuring that the digital “address” of the hotel cannot be redirected to a fraudulent server.
-
Encrypted Payment Gateways: Utilizing Level 1 PCI-compliant systems that never store full card details on-site.
-
Identity Verification (IDV): Using biometric or blockchain-verified ID checks before high-value transactions are finalized.
-
Brand Monitoring Services: Automated scans of social media and search engines for fraudulent advertisements.
-
Redundant Server Hosting: Maintaining separate, synchronized servers in different geographic regions to prevent downtime-based vulnerabilities.
-
Sovereign Data Storage: On-site, encrypted backups that allow the property to operate its critical booking systems for 72 hours without external cloud access.
-
Predictive Fraud Analysis: Software that tracks the “metabolic rate” of booking attempts to identify bot-driven attacks.
-
Digital Twins of the Transaction Flow: Real-time 3D models of the hotel’s informational architecture used for remote troubleshooting by senior security engineers.
Risk Landscape and Failure Modes
The most dangerous risk in elite hospitality management is compounding fragility. This occurs when multiple minor environmental stressors fail simultaneously, overwhelming the management layer. For example, a minor server lag might disable the SSL certificate, which in turn triggers browser warnings, which then allows a scammer to provide a “workaround” link to a desperate guest during a holiday weekend.
A systemic approach requires a taxonomy of procurement risk:
-
Terminal Risks: Total loss of financial control, mass data breach of high-net-worth iindividuals permanent blacklisting by payment processors.
-
Operational Risks: Domain hijack, primary gateway breach, API integration failure.
-
Frictional Risks: Minor phishing emails, localized sensor calibration drift, suspicious login attempts.
The goal of the property steward is to ensure that no frictional risk ever compounds into an operational or terminal risk.
Governance, Maintenance, and Long-Term Adaptation
A wellness asset is a dynamic system that requires a living document of governance. This document must survive both the owner and the manager.
-
Biannual Security Audits: Measuring the integrity of the encryption layers and the vulnerability of the human staff to social engineering.
-
Annual Protocol Reviews: Measuring the accumulation of “digital debt” in secondary software integrations to adjust security cadences.
-
The 10-Year Resilience Plan: Anticipating global shifts in digital identity and ensuring the building’s infrastructure can adapt to new cryptographic technologies.
Governance means treating the hotel as a corporate entity with its own board, its own audits, and its own long-term strategy for survival in a volatile digital climate.
Measurement, Tracking, and Evaluation
How do we measure the success of an invisible operation? We look at leading indicators rather than lagging indicators.
-
Leading Indicator: 100% completion rate of weekly password rotations and API key refreshes.
-
Lagging Indicator: The hotel didn’t lose money last month. This is often luck, not strategy.
-
Qualitative Signal: The inhabitant reports that the booking process felt “rigorous but secure” despite the high financial stakes.
-
Quantitative Signal: The Mean Time Between Attempts (MTBA) for bot-driven fraud is increasing year-over-year.
Documentation examples include the Metabolic Health Ledger, a monthly report detailing every server spike, data anomaly, and transactional shift.
Common Misconceptions and Oversimplifications
-
Myth: High-end sites are “too big to be spoofed.” Correction: Scammers prioritize high-value targets because a single successful breach yields massive returns.
-
Myth: “https://” means the site is legitimate. Correction: SSL certificates only mean the connection is encrypted; they do not verify the identity of the person holding the certificate.
-
Myth: Luxury means “effortless booking.” Correction: True luxury means an engineered environment where the safety of the inhabitant’s data is prioritized over the speed of the transaction.
-
Myth: Bank transfers are safer than credit cards. Correction: Bank transfers are often irreversible, making them the preferred tool for high-fidelity scams.
-
Myth: Security can be handled by a general IT staff. Correction: Property owners create technical debt when they employ non-specialized labor for high-fidelity cryptographic systems.
-
Myth: A single firewall is sufficient. Correction: Firewalls are static; a sovereign security layer must be dynamic and redundant.
Ethical and Practical Considerations
The rise of high-fidelity hospitality nodes brings a responsibility to the local human and ecological ecosystem. A hotel that operates as a hardened, resource-hungry island risks becoming a target of local resentment. The most resilient security strategies practice social integration,n utilizing local, high-shelf-life training programs that reduce the property’s “informational footprint” and support the regional digital economy.
Furthermore, we must consider the human capital involved. The most effective stewards are those who are treated as professional technicians rather than seasonal workers. Investing in specialized training for staff regarding social engineering mitigation creates a knowledge firewall that is far more effective than any physical barrier.
Conclusion: Synthesis and Adaptability
The architecture of the luxury wellness market has shifted permanently toward the sovereign node. Success in this field no longer depends on the beauty of the design or the variety of the treatment menu. It depends on the integrity of the underlying systems, the metabolic health of the site, the digital sovereignty of the network, and the resilience of the maintenance protocols.
By applying the principles of high-fidelity stewardship, the modern developer moves beyond the era of reactive repair into an era of structural utility. The goal is not merely to provide a bed and a massage, but to govern a resilient environment that facilitates human performance and biological recovery. In an increasingly volatile global landscape, the well-managed sanctuary is the ultimate firewall, a sanctuary where the complexities of the environment are managed so effectively that they become, quite literally, invisible.